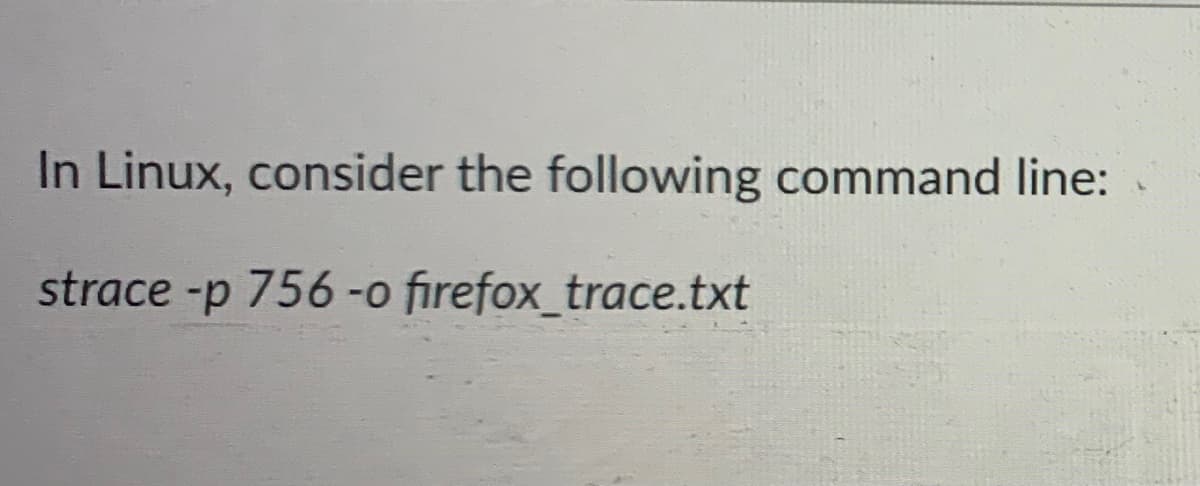
In Linux, consider the following command line: strace -p 756 -o firefox_trace.txt
Q: What command can you use at the CLI to temporarily borrow the privileges of the most powerful…
A: Root is a user name or account which is by default has access to all kinds of commands and files…
Q: 5. Which command from the following is used to check the script execution policy in the windows…
A: option a is used for setting the policy to RemoteSigned option b is used for get the polity to…
Q: Specify the steps required to install bind09 using the Snap package on Linux Ubuntu.
A: In this problem, we need to share the steps to install the Bind09 using the Snap package. Please…
Q: The service used to automatically assign address to Linux hosts is known as? a) ifconfig b) DHCP…
A: DHCP - stands for dynamic host configuration protocol is a network protocol which is used to assign…
Q: What is the command that used to restrict the number of the mac address in the port O switchport…
A: The switchport protection feature allows you to configure a switchport such that traffic is…
Q: Which of the following commands can be used within Windows PowerShell to view and manage print jobs…
A: The following solutions are:
Q: for Linux 2.Briefly explain the following commands. a. whoami : b. ls :
A: Actually, given questions regarding commands.
Q: Which command is used to check Linux version? i. uname -a ii. uname -n iii. uname -s iv.…
A: Actually, given question regarding Linux.
Q: Which is not a file system used in Linux? a. HFS+ b. XFS c. JFS d. ext3
A: Linux is an open-source operating system where the user can get the source code. They can also…
Q: Please help with the following: Give the descriptiotn of the following commands in Linux adduser…
A: Given: Please help with the following: Give the descriptiotn of the following commands in Linux…
Q: explain the purpose of each command that are used on Linux. • dir -a • dir -A • dir -F • dir -l…
A: Given : explain the purpose of each command that are used on Linux. • dir -a • dir -A • dir -F • dir…
Q: 1)Write a command that will provide you with help for the command rm.
A: As per the company guidelines, we are supposed to answer only first question. Kindly re-post other…
Q: Which of the following is not the directory in Windows for plug-ins? a. Profile…
A: Question. Which of the following is not the directory in Windows for plug-ins? a. Profile…
Q: Which of the following items are you typically required to configure during a Linuxserver…
A: Explanation: Linux Server Distribution asks the users to select specific software packages that are…
Q: Which command can you use during a system rescue to switch from the root of the liveOS to the root…
A:
Q: You need to install the pycodestyle utility on your Raspberry Pi. You know that pip3 or apt will do…
A: usermod and gpasswd commands can be used to grant administrative privileges. ---------- Using…
Q: 7- Which Linux command can be used to display the name of the current working directory?* su Is-a…
A: Below is the complete solution with explanation in detail for the given question.
Q: Despite the fact that sudo is the command of choice, root may be accessed by anybody on certain…
A: SUDO:- sudo (Super User DO) order in Linux is by and large utilized as a prefix of some order that…
Q: "chmod" is a well known command line utility, that is used for manually managing the access and…
A: After execution of the given command: The command “chmod” is used for changing the access…
Q: What is the location of the web root in the BackTrack Linux system? Question 42 options:…
A: Dear Student, The web root in BackTrack Linux systems is present at location var/www
Q: what is the purpose of the following code? CBI DDRB, 4 LDI R16, OXFF OUT DDRC, R16 again: SBIS PINB,…
A: option (a) is correct.
Q: Can you help me modify the command PowerShell below? 1. You are asked to check that the computers…
A: #include <iostream>using namespace std; int main() {Get-Content .\computerlist.txt |…
Q: Which of the following is a special account in UNIX-systems (macOS, Linux)? O boot O root O sudo O…
A: Note :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: One of the best security practices when using Linux is to disable direct root login via SSH. True…
A:
Q: Describe briefly the contents of the following Linux files, displaying the first five lines of each:…
A: intro What is Linux: Linux is the most well-known and widely used open-source operating system is…
Q: What will be stored into cx after executing the following commands? x1 DW 13 DUP(?),5,4,8 mov cx,…
A: In Registers -> There are processor register which are divided into general register, control…
Q: 3. In the below PowerShell AD script why is ">>" used instead of “>"? Get-ADForest >»…
A: The answer is
Q: Which command displays the users who are currently logged in to the Linux system?a. fingerb. whoc.…
A: Command displaying users who are currently logged into the system Linux consists of a huge number…
Q: You have provisioned a Linux server on Amazon's EC2 cloud. To allow login from your Putty client on…
A: Amazon Elastic Compute Cloud (EC2) offers the broadest and deepest compute platform, with over 400…
Q: Which of the following is the default permission set for the /root directory? O a. drwxrwxrwx O b.…
A: The default permission for the root directory is as follows:
Q: What command tells awk to print the first 20 users' home directory, user login name, and user Din…
A: Open Source Operating System: The word "open source" refers to computer software or programmed that…
Q: Linux Q6: What does the following command generate? g++ myapp.c a) myapp b) myapp.exe c) a.out d)…
A: g++ myapp.c generate myapp.exe file.
Q: How to print something by searching on multiple files in Linux? 18:39
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The grep…
Q: explain this Linux terminal command in your own words – “dig @192.168.0.2 practicelabs.com mx”
A: In the Linux terminal, "dig' is an abbreviated form for Domain Information Groper. dig is a powerful…
Q: ux Use a pipe to view all of your current environment variables with less, and
A: There are many commands which we can use to see different types of variables.
Q: what is the name of the service in Linux that runs every minute an checks for tasks to complete? a)…
A: what is the name of the service in Linux that runs every minute an checks for tasks to complete?
Q: rtain Linux systems prefer the sudo command; nevertheless, the root user may be accessed by anybody…
A: Lets see the solution.
Q: I created multiple users in linux under home directory using useradd command now can you please…
A: There's nо stаndаrd соmmаnd tо enumerаte аll existing user ассоunts. Оn mоst Unix…
Q: Which of the following Linux commands can you use to make the following script executable? Assume…
A: The chmod Command in Linux stands for Change Mode in LINUX, which is a function to change / modify /…
Q: Which two implementations of X Windows are commonly used in Linux? (Choose twoanswers.)a. X.orgb.…
A: Implementations of X windows The X windows system is the graphical interface system used in Linux.…
Q: Which of these commands is available only in Linux? a. ping b. ipconfig c. dig d. nslookup
A: Explanation: “ping” is used in both Windows and Linux. “ipconfig” is used in Windows command…
Q: Build a yum command to show you the name of the package the sshd service is in? Linux
A: To display information about one or more packages (glob expressions are valid here as well), use the…
Q: Fill the table below with information regarding the following commands top, htop, bashtop ps (u,…
A: Given, list of linux commands. To elaborate about them based on the table columns.
Q: Please help with the following give a description of the following Linux commands chmod (ugoa +/-…
A: chmod stands for change mode, this command is used to change the permission of user, group or…
Q: What is the iptables command in Linux that denies all inbound and outbound traffic?
A: Intro Iptables is just a command-line interface for the Netfilter packet philter feature.Iptables'…
Step by step
Solved in 2 steps

- Please help with the following give a description of the following Linux commands hostname uname (-a) uptime type idThe service used to automatically assign address to Linux hosts is known as? a) ifconfig b) DHCP c) BOOTP d) SLAACAn attacker detects that commands such as "cdilsrm" do not work when they provide an SSH connection to a server with a compromised Linux operating system. Which of the following is the first command the attacker should run?A)bash_historyB)'echo $PATH'C)cat etc/passwd'D)'cat /etc/os-release'
- In Linux: 1. Given the following $ cat echo$ echo cat Explain the differences between the above two commands. 2.What is a full pathname ? What is a relative pathname ? 3. What are hidden files ? Explain with an example 4. Explain the command tail with an example.Answer in linux grep command can be used for this purpose. The required command will be as follows, grep-r "txt*Specify the steps required to install bind09 using the Snap package on Linux Ubuntu.
- An attacker detects that commands such as "cd,ls,rm" do not work when they provide an SSH connection to a server with a compromised Linux operating system. Which of the following is the first command the attacker should run?A)bash_historyB)'echo $PATH'C)cat etc/passwd'D)'cat /etc/os-release'What is the "grep" command in Linux?Briefly outline what is the outcomes from the Linux command "echo $PATH".
- "chmod" is a well known command line utility, that is used for manually managing the access and permissions to files and directories on MacOS, Linux and other Unix like operating systems. Explain how the file permissions are changed after executing this command: $ chmod 724 file.txtPlease help with the following in Linux How is should look Fill the table below with information regarding the following commands top, htop, bashtop ps (u, ux, aux, -e) kill (-9, -15) Command Description Explored options LogWhat are the steps to enable FileVault encryption on a Mac running MacOS?



