Java Very important: As a COMMENT IN CODE, please DO Test-Cases on how you would test your solution assumptions and hence your code explore a specific way to perform a Breadth First Search (BFS) of a given Graph [Ref : Figure 1].
Q: What is the definition of an intranet?
A: Introduction: An intranet is a private network within a firm that allows employees to exchange…
Q: Identify important benefits, as well as concerns and issues, related to educational information…
A: Educational information systems: An information system is a collection of interconnected parts or…
Q: Create -commerce
A: The program is written in HTML and CSS. Check the program screenshot for the correct indentation.…
Q: What services does the physical layer provide?
A: Introduction: The physical layer provides the following services:
Q: he many types of netw
A: Depending on the network's physical layer, topology, and size, many types of network cables are…
Q: Example-3: Write a program to calculate the Area and volume for a sphere. Scl. -The area of sphere 4…
A: Given: The program is written in C language to find area and volume of sphere.
Q: Write a 2 page report on how Google Dorking can used for good and evil.
A: A Google dork query, also known as a dork, is a search string that uses sophisticated search…
Q: Computer science What are the quality assurance practices used for preparing components models?
A: Introduction Component models are used to define certain properties satisfied by components, and…
Q: Online sellers do a variety of tasks such as take photograph and write descriptions of the items…
A: We need to discuss how factors such as the CPU and RAM affect system performance. And, advise on…
Q: For the following questions, perform the operations in sequence. So, for example, part (b) should…
A:
Q: Question 11 Identify the vertex that is adjacent to E. A D E B.
A: Ans: The vertex that is adjacent to E is: The adjacent vertex for E is E -> C E -> B
Q: What must be true about valid equals() and hashCode() methods? O 01.equals(02) = o1.hashCode() ==…
A: Answer:- o1.equals(o2) => o1.hashcode() == o2.hashcode() !o1.equals(o2) =>…
Q: In comparison to hardware-defined networking, what are the two most significant benefits of software…
A: Networking: It is defined as the process of establishing contact and exchanging information with…
Q: Explain the last data pointer register in simple terms.
A: Solution: Register of data pointersIt is a 16-bit register that stores values in two bytes. DPTR is…
Q: What is it about virtual memory that prevents it from being employed more frequently in embedded…
A: INTRODUCTION: Here we need to tell about virtual memory that prevents it from being employed more…
Q: In your own words describe what is Social Media Phishing?
A: Please find the detailed answer in the following steps.
Q: What type of software does each of the following: word processing programs, spreadsheet programs,…
A: Software : The program is a collection of instructions for doing a given activity. The software…
Q: How memory-efficient is a COM program when it's running
A: Component object model (or program) The Common Object Module (COM) file format represents executable…
Q: Many firms are beginning to make advantage of big data these days. Discuss how it is used by the…
A: Big data is a term that refers to a collection of unstructured, semi-structured, and structured data…
Q: le the implementation of local search. (Intelligent artificial course)
A: A local search algorithm begins from an arbitrarily picked total launch and moves starting with one…
Q: Which attacks are downgraded and how can you defend?
A: In a downgrade attack, an attacker compels a network channel to switch to an unprotected or less…
Q: VLAN is intended to provide administrative access to netwc
A: Below the VLAN is intended to provide administrative access to network devices
Q: only python Your program should ask the user to input a number of family members. The program should…
A: Solution: Code: def ask_for_age(): age = int(input('Enter the age of a family member: '))…
Q: :the output of (Print "a", "b", "c") is abc O ab c abc
A: The print() function prints the specified message to the screen. The message can be a string, or any…
Q: What are the two key benefits of Software Defined Networks over Hardware Defined Networks, and how…
A: Still to be determined: Software Defined Networking, or SDN, is a networking technology that…
Q: Computer science What is Artificial Intelligence's goal? Give two instances for each of the…
A: Introduction: Artificial intelligence (AI) uses techniques such as machine learning and deep…
Q: As a computer maker, you confront the difficulty of creating high-quality computers with fast…
A: Introduction: The number of cycles/seconds that a central processor works is referred to as…
Q: The router layer 2 protocol has been found to contain a number of flaws. In a PPP encapsulated…
A: Layer 2 Protocol Issues In the OSI architecture, the Data LInk layer is the second layer. It is…
Q: Explain the meanings of the phrases CRUD and RESTful.
A: answer is
Q: Which of the following is a treap? H R 45 22 38 b. 78 N H 45 28 M 38
A: The right answer will be option(a) Explanation:- A treap is a combination of tree+heap(binary tree)…
Q: Give a detailed explanation of the relational model using an appropriate example.
A: The relational model is an abstract paradigm for organizing and managing data in a database. It…
Q: What methods are in place to deal with resource hogging?
A: Resource hogging: resource hog (plural resource hogs) is a noun (computing, slang) When compared to…
Q: Q1.) Write a Review class that has: • These private data members: • string user: ID of the user…
A:
Q: Write a Java public static general method which doesn't belong to Queue class(assuming the Queue…
A: The Answer start from step-2.
Q: use four ways to run python,
A: 1. Interactive way: Install python in your system. Open cmd ( command Lime ) Type "python" Now ,…
Q: .. Write a CPP program that reads a line consists of an unknown number of words. The program then…
A:
Q: What is IP Address Management, and how does it work?
A: Introduction: IP Address Management (IPAM) is a system for organising, tracking, and managing…
Q: Why is it so difficult to use virtual memory in embedded systems?
A: Introduction: Virtual memory is a feature of many operating systems that allows applications to…
Q: Although the BCNF method guarantees lossless decomposition, it is conceivable to have a schema and a…
A: Introduction: It is feasible to have a lossless decomposition into 3NF itself instead of BCNF. It is…
Q: Do data structures and algorithms become outdated in the era of Machine Learning?
A: Machine learning : It is not true that algorithms and data structures are no longer needed in the…
Q: In what circumstances do you think assembly language code should be used in the creation of an…
A: Assembly language : An assembly language is a low-level programming language used to communicate…
Q: Create ASM statements that, when the left mouse button is pressed, cause the cursor to jump to label…
A: Introduction: Content is its content property. Take care of the Button Base. When a user clicks a…
Q: What is an IP address and what role does it play in a computer network system?
A: Introduction: A computer's internet protocol (IP) address allows it to send and receive data over…
Q: Assume that two students are attempting to enroll in a course for which only one seat is available.…
A: Database Systems, also known as DBMS, is software that collects electronic and digital records to…
Q: 2. Using suitable command encode the message "Your Name" by using matrix A given below: [1 2 31 A =…
A: Find the required code in matlab and output given as below :
Q: A null bitmap is used in the variable-length record format to indicate whether an attribute has a…
A: Offset: The term "offset" refers to the distance between two points or memory locations in computer…
Q: Short answer Computer science Name two major differences between IPV4 and IPV
A: Introduction: The following are the distinctions between IPv4 and IPv6:
Q: What are application layer hijacking tools and session hijacking tools?Compare and contrast the…
A: Introduction: A cyber hijacking attack is a form of network security attack in which the attacker…
Q: Explain the application programming interface in a few words (API)
A: Start: An application programming interface, sometimes known as an API, allows businesses to make…
Q: in cpp Write a function to count the number of blank spaces in a text file named "input.txt"
A: Use an ifstream to stream the file contents and keep on reading as long as there are contents in…
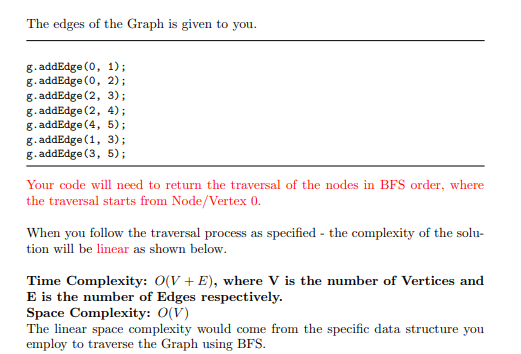
Java
Very important: As a COMMENT IN CODE, please DO Test-Cases on how you would test your solution assumptions and hence your code
explore a specific way to perform a Breadth First Search (BFS) of a given Graph [Ref : Figure 1].
![2
4
5
Figure 1: Graph for Traversal
/* Class representing a directed graph using adjacency lists */
static class Graph
int V; //Number of Vertices
LinkedList<Integer> [] adj; // adjacency lists
//Constructor
Graph (int V)
{
this.V = V;
adj - new LinkedList [V];
for (int i = 0; i < adj.length; i++)
adj [i] = new LinkedList<Integer>();
//To add an edge to graph
void addEdge (int v, int w)
{
adj [v].add (w); // Add w to the list of v.
2](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fc353cc0f-0c4d-4d5b-a3e6-e746dbb90f94%2Fc1ec10d4-623b-4583-9739-3468d00f5c87%2Fppcc0q_processed.png&w=3840&q=75)
Trending now
This is a popular solution!
Step by step
Solved in 5 steps with 4 images

- Implement class “LinkedList” which has two private data members head: A pointer to the Node class length: length of the linked listImplement the following private method:1. Node* GetNode(int index) const;A private function which is only accessible to the class methods. . For example, index 0 corresponds to the head and index length-1 corresponds to end node of the linked list. The function returns NULL if the index is out of bound.Implement the following public methods:2. LinkedList();Constructor that sets head to NULL and length equal to zero.3. bool InsertAt(int data, int index);Insert a new node at the index. Return true if successful, otherwise,return false. The new node should be at the position “index” in the linked list after inserting it. You might have to use GetNode private function. these 3 partsImplement a Single linked list to store a set of Integer numbers (no duplicate) • Instance variable• Constructor• Accessor and Update methods 2.) Define SLinkedList Classa. Instance Variables: # Node head # Node tail # int sizeb. Constructorc. Methods # int getSize() //Return the number of nodes of the list. # boolean isEmpty() //Return true if the list is empty, and false otherwise. # int getFirst() //Return the value of the first node of the list. # int getLast()/ /Return the value of the Last node of the list. # Node getHead()/ /Return the head # setHead(Node h)//Set the head # Node getTail()/ /Return the tail # setTail(Node t)//Set the tail # addFirst(E e) //add a new element to the front of the list # addLast(E e) // add new element to the end of the list # E removeFirst()//Return the value of the first node of the list # display()/ /print out values of all the nodes of the list # Node search(E key)//check if a given…Implement a Single linked list to store a set of Integer numbers (no duplicate) • Instance variable• Constructor• Accessor and Update methods 1. Define a Node Class.a. Instance Variables # E element- (generics framework) # Node Next (pointer) - refer to the next node (Self-referential)b. Constructorc. Methods # E getElement() //Return the value of this node. # setElement(E e) // Set value to this node. # Node getNext() //Return the pointer of this node. # setNext(Node n) //Set pointer to this node. # displayNode() //Display information of this node.
- Implement a Doubly linked list to store a set of Integer numbers (no duplicate) • Instance variable• Constructor• Accessor and Update methods2. Define DLinkedList Classa. Instance Variables: # Node header # Node trailer # int sizeb. Constructorc. Methods # int getSize() //Return the number of nodes of the list. # int getSize() //Return the number of elements of the list. # boolean isEmpty() //Return true if the list is empty, and false otherwise. # E getFirst() //Return the value of the first node of the list. # E getLast()/ /Return the value of the Last node of the list. # addFirst(E e) //Add a new node to the front of the list. # addLast(E e) //Add a new node to the end of the list. # Node remove(Node n) //remove a node which has the reference n from the list # Node removeFirst() //Remove the first node of the list, and return the removed node or null if failed. # Node removeLast() //Remove the last node of the list, and return the…Implement a Doubly linked list to store a set of Integer numbers (no duplicate) • Instance variable• Constructor• Accessor and Update methods1. Define a Node Class.a. Instance Variables # E element - (generics framework) # Node next (pointer) - refer to the next node (Self-referential) # Node prev (pointer) - refer to the previous node (Self-referential)b. Constructorc. Methods # E getElement() //Return the value of this node. # setElement(E e) // Set value to this node. # Node getNext() //Return the next pointer of this node. # setNext(Node n) //Set the next pointer to this node. # Node getPrev() //Return the pointer of this node. # setPrev(Node n) //Set the previous pointer to this node. # displayNode() //Display the value of this node.package circularlinkedlist;import java.util.Iterator; public class CircularLinkedList<E> implements Iterable<E> { // Your variablesNode<E> head;Node<E> tail;int size; // BE SURE TO KEEP TRACK OF THE SIZE // implement this constructorpublic CircularLinkedList() {} // I highly recommend using this helper method// Return Node<E> found at the specified index// be sure to handle out of bounds casesprivate Node<E> getNode(int index ) { return null;} // attach a node to the end of the listpublic boolean add(E item) {this.add(size,item);return false; } // Cases to handle// out of bounds// adding to empty list// adding to front// adding to "end"// adding anywhere else// REMEMBER TO INCREMENT THE SIZEpublic void add(int index, E item){ } // remove must handle the following cases// out of bounds// removing the only thing in the list// removing the first thing in the list (need to adjust the last thing in the list to point to the beginning)// removing the last…
- Implement a LinkedList class that stores integers using dynamic memory and a proper main program to test it. The following member functions need to be properly implemented and tested: 1. Default constructor. 2. Parmetrized Constructor. 3. Sum. 4. Average. 5. InsertAtHead. 6. InsertAtTail. 7. Delete. 8. Pop. 9. Circular. 10. Display. Sample answer is also provided.Computer Science Java Programming ******* Write a Java application that will, given an appropriate data structure, will be able to track the following module and its dependencies as well as implement an appropriate search algorithm to create the correct graph for any given module. The graph will show all the corresponding dependent modules in their correct order of dependency. Must use Stack, either Double ArrayList or Linked List, and simple search to implement this. Module A: Dependencies: B D E K L Module B: Dependencies: F G M Module C: Dependencies: F Module D: Dependencies: G Module E: Dependencies: B A Module F: Dependencies: B Module G: Dependencies: NONE Module K: Dependencies: M Module L: Dependencies: Q Module M: Dependencies: A Module Q: Dependencies: NONE Ensure that dependencies are only visited only once. To test: Input A Your Output: Module A. Dependencies: B F G M D E K M L QA) Write a generic Java queue class (a plain queue, not a priority queue). Then, call it GenericQueue, because the JDK already has an interface called Queue. This class must be able to create a queue of objects of any reference type. Consider the GenericStack class shown below for some hints. Like the Stack class below, the GenericQueue should use an underlying ArrayList<E>. Write these methods and any others you find useful: enqueue() adds an E to the queue peek() returns a reference to the object that has been in the queue the longest, without removing it from the queue dequeue() returns the E that has been in the queue the longest, and removes it from the queue contains(T t) returns true if the queue contains at least one object that is equal to t *in the sense that calling .equals() on the object with t the parameter returns true.* Otherwise contains returns false. size() and isEmpty() are obvious.
- Implement class “LinkedList” which has two private data members head: A pointer to the Node class length: length of the linked list // Node* GetNode(int index) const;A private function which is only accessible to the class methods. This function takes an array-like index and returns the address of the node at that index. For example, index 0 corresponds to the head and index length-1 corresponds to end node of the linked list. The function returns NULL if the index is out of bound.// Implement the following public method: 1. bool RemoveHead();// Use RemoveAt FunctionRemove first node. Return true if successful, otherwise, false.2. bool RemoveEnd();// Use RemoveAt FunctionRemove last node. Return true if successful, otherwise, false.3 . void DisplayList() const;Display data of the whole linked list this in c++.Complete the method to perform breadth first traversal (search) here is the method: private static void breadthFirst() { //Todo System.out.println("test"); }here is the complete source code: Graph.java---------------------------------package finlab;import java.util.*;public class Graph { List<Edge>[] list; public Graph(int n){ list = new LinkedList[n]; for(int i=0; i<list.length;i++){ list[i] = new LinkedList<>(); } } void addEdge(int u, int v, int w){ list[u].add(0,new Edge(v,w)); } boolean isConnected(int u, int v){ for(Edge e: list[u]) { if (e.v == v) return true; } return false; } @Override public String toString(){ String result= ""; for(int i=0; i<list.length; i++){ result+= i+": "+list[i]+"\n"; } return result; }}Edge.java--------------------------------------------------------package…Create a class Queue and a Main class. This queue will be implemented using the LinkedList class that has been provided. This queue will hold values of a generic type (<T>). Your Queue should have the following public methods: public void enqueue(T data) public T dequeue() public T peek() public int size() public boolean isEmpty() public class LinkedList<T> { private Node<T> head; private Node<T> tail; private int size; @Override public boolean isEmpty() { return size == 0; } @Override public void append(T data) { Node<T> node = new Node<>(data); if (tail == null) { head = tail = node; } else { tail.next = node; node.prev = tail; tail = node; } size++; } @Override public void prepend(T data) { Node<T> node = new Node<>(data); if (head == null) { head = tail = node; } else {…

